Modern Exposure Management for Today’s Expanding Digital Environments
Cyber threats continue to evolve as organizations rely more on cloud platforms, remote access, and digital operations. Exposure management focuses on identifying, prioritizing, and reducing security weaknesses across all digital assets. Instead of waiting for attacks, businesses can continuously evaluate their cyber risks and strengthen their defenses. This approach helps organizations improve visibility, maintain compliance, and reduce the likelihood of costly breaches while supporting long-term operational stability.
Protecting Small Businesses Through Proactive Cyber Risk Visibility
Exposure Management for SMBs helps smaller organizations identify security gaps that attackers often target. Limited budgets and IT staff make it difficult to track vulnerabilities manually. With structured exposure management, small businesses gain better insight into where their risks exist and how to fix them efficiently. This allows leadership teams to focus on growth without constantly worrying about cyber threats disrupting their operations.
- Identifies exposed cloud services and remote access points
- Highlights unpatched software and outdated systems
- Prioritizes vulnerabilities based on real-world risk
- Helps small teams manage security with limited resources
Scalable Security Control for Multi Client Managed Service Providers
Exposure management for MSPs enables service providers to oversee multiple client environments through a unified risk framework. By maintaining centralized visibility into vulnerabilities and external exposures, MSPs can deliver stronger security outcomes. This approach allows providers to detect threats early, reduce customer downtime, and build trust by offering proactive protection instead of reactive incident handling.
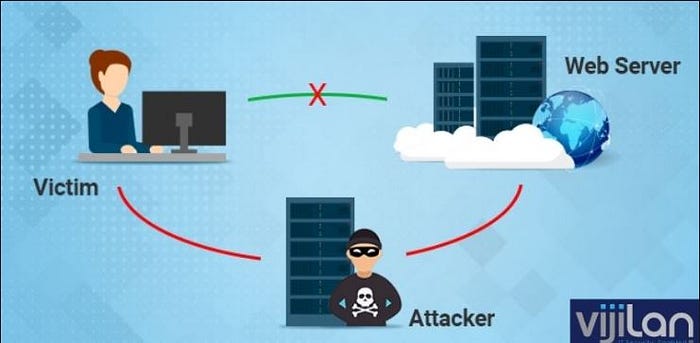
Identifying Hidden Risks Across Expanding Digital Attack Surfaces
Attack surface management services help organizations locate unknown or forgotten digital assets that could become entry points for attackers. As companies add cloud workloads, third-party integrations, and remote systems, their attack surface grows. Continuous discovery ensures that security teams know what must be protected, reducing blind spots that hackers could exploit.
- Detects unmanaged websites and cloud assets
- Finds exposed applications and open network ports
- Monitors third-party and shadow IT risks
- Helps close security gaps before attackers exploit them
Reducing Cyber Threats Using Structured Vulnerability Management Programs
Managed vulnerability management ensures that security weaknesses are identified, evaluated, and prioritized on an ongoing basis. Instead of treating every vulnerability equally, organizations can focus on those most likely to be exploited. This reduces overall exposure and makes remediation efforts more efficient, especially in environments with thousands of assets.
Maintaining Constant Awareness Through Continuous Cyber Risk Monitoring
Continuous exposure management provides real-time insight into new vulnerabilities and changes across the IT environment. As systems are updated, added, or removed, security risks shift. Continuous monitoring ensures that no new exposure goes unnoticed, allowing teams to respond quickly and keep defenses aligned with evolving infrastructure.
Tracking Public Facing Assets Through External Attack Surface Monitoring
External attack surface monitoring focuses on everything an attacker can see from the internet. This includes web applications, cloud services, and remote access tools. By understanding what is publicly exposed, organizations can minimize their digital footprint and eliminate unnecessary risks that could lead to breaches.
- Monitors open ports and exposed services
- Identifies vulnerable public-facing applications
- Helps reduce internet-based attack vectors
- Improves perimeter security visibility
Prioritizing Security Efforts Using Risk Based Vulnerability Management
Risk-based vulnerability management allows organizations to fix the most dangerous issues first. Rather than reacting to long lists of vulnerabilities, security teams focus on threats that could realistically be exploited. This approach improves security efficiency while lowering the likelihood of major cyber incidents.
Ensuring Healthcare Data Safety Through HIPAA Aligned Security Controls
HIPAA vulnerability management supports healthcare organizations in protecting patient records and clinical systems. By identifying weaknesses in electronic health records, medical devices, and connected networks, healthcare providers can prevent data breaches and meet strict compliance requirements designed to safeguard sensitive information.
Strengthening Financial Sector Resilience Through Exposure Risk Management
Financial services exposure management helps protect transaction platforms, customer portals, and digital banking systems. By monitoring vulnerabilities and internet-facing assets, financial institutions can reduce fraud risks, protect sensitive financial data, and ensure stable, secure operations in a highly regulated environment.
Protecting Industrial Networks With Manufacturing Exposure Management Strategies
Manufacturing exposure management focuses on securing production systems, operational technology, and connected industrial devices. By identifying vulnerabilities in factory networks, manufacturers can prevent cyber incidents that might disrupt operations, damage equipment, or compromise intellectual property.
Conclusion
Exposure management is essential for modern organizations seeking to stay ahead of cyber threats. By combining attack surface visibility, vulnerability tracking, and continuous risk monitoring, businesses can reduce their exposure and strengthen their defenses. Whether supporting small businesses, service providers, healthcare, financial services, or manufacturing, a proactive exposure management strategy ensures long-term security, compliance, and operational resilience.
FAQs
Q. What is exposure management in cybersecurity?
A. It is the process of identifying, prioritizing, and reducing security weaknesses across all digital assets.
Q. How does exposure management help small businesses?
A. It gives small organizations visibility into risks so they can fix the most dangerous issues first.
Q. Why is continuous monitoring important?
A. Because IT environments change constantly, and new vulnerabilities can appear at any time.
Comments
Post a Comment