Modern Exposure Management Strategies for Growing and Regulated Organizations
As cyber risks continue to expand beyond traditional network boundaries, organizations must move from reactive security practices to proactive exposure-focused strategies. Businesses across industries now rely on continuous visibility, prioritization, and remediation to reduce risk across digital assets, cloud services, and external-facing systems while maintaining compliance and operational resilience.
Proactive Risk Reduction for Smaller Organizations
Exposure Management for SMBs focuses on identifying, assessing, and prioritizing security gaps that attackers are most likely to exploit. Small and mid-sized businesses often operate with limited resources, making it essential to focus on the most impactful exposures. Key advantages include:
- Clear visibility into high-risk assets and misconfigurations
- Prioritized remediation based on business impact
- Reduced attack paths with limited security resources
Scalable Security Oversight for Service Providers
Exposure management for MSPs enables managed service providers to continuously evaluate risk across multiple client environments using centralized workflows. This approach improves consistency, reporting, and service scalability while helping MSPs demonstrate measurable security outcomes to customers without increasing operational complexity.
Visibility Across Digital Entry Points
Attack surface management services provide continuous discovery and monitoring of internet-facing assets, shadow IT, and cloud services. Organizations gain a clearer understanding of how attackers may view their environment, enabling proactive risk reduction. Key capabilities include:
- Discovery of unknown or unmanaged assets
- Monitoring of exposed services and domains
- Early detection of misconfigurations and risks
Addressing Weaknesses Before Exploitation
Managed vulnerability management shifts security programs from periodic scanning to continuous assessment and remediation. By identifying vulnerabilities early and tracking remediation progress, organizations can significantly reduce exposure windows and prevent exploitation that often results from delayed patching and incomplete visibility.
Continuous Assessment in Dynamic Environments
Continuous exposure management ensures security posture is evaluated in real time as infrastructure changes occur. This approach is especially valuable in cloud and hybrid environments where assets and configurations change frequently, allowing organizations to detect and address emerging risks before they escalate.
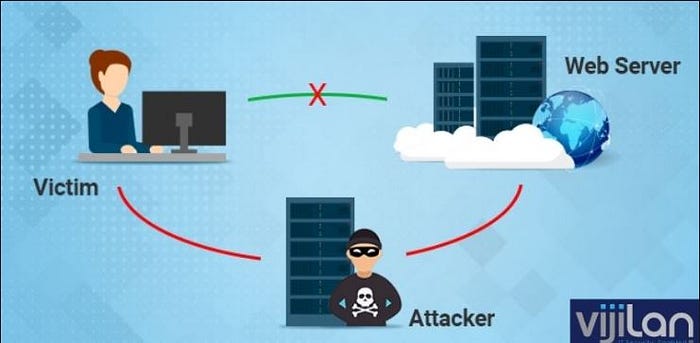
Monitoring Threats Beyond the Network Perimeter
External attack surface monitoring focuses on identifying exposed services, credentials, and misconfigurations visible from the internet. By continuously assessing external-facing assets, organizations can reduce reconnaissance opportunities and lower the risk of targeted attacks. Benefits include:
- Reduced blind spots across external assets
- Faster identification of publicly exposed risks
- Improved alignment with threat intelligence
Prioritizing What Matters Most
Risk-based vulnerability management emphasizes remediation decisions based on exploitability, threat context, and potential business impact. This approach allows security teams to focus on critical issues rather than overwhelming vulnerability lists, improving efficiency and strengthening overall security outcomes.
Protecting Sensitive Healthcare Systems
HIPAA vulnerability management supports the identification and remediation of weaknesses that could expose electronic health information. Healthcare organizations rely on structured vulnerability programs to maintain compliance, demonstrate due diligence, and protect patient data without disrupting essential clinical operations.
Securing High-Value Financial Environments
Financial services exposure management addresses risks associated with payment systems, customer data, and regulated financial platforms. Continuous exposure visibility helps financial organizations reduce fraud risk, meet regulatory expectations, and maintain trust while operating in highly targeted threat environments.
Reducing Risk in Industrial and Production Systems
Manufacturing exposure management focuses on minimizing cyber risk across operational technology, production networks, and connected systems. As manufacturing becomes more digitally connected, continuous exposure monitoring helps prevent downtime, protect intellectual property, and maintain safe, uninterrupted operations.
Conclusion
Exposure management enables organizations to shift from reactive security measures to proactive risk reduction. By adopting continuous visibility, prioritization, and remediation strategies, businesses and service providers can strengthen security posture, support compliance, and improve resilience against evolving cyber threats.
FAQs
1. What is exposure management in cybersecurity?
A. Exposure management focuses on identifying, prioritizing, and reducing security risks that attackers are most likely to exploit.
2. How does exposure management differ from traditional vulnerability scanning?
A. Exposure management is continuous and risk-based, while traditional scanning is periodic and often lacks prioritization.
3. Why is exposure management important for regulated industries?
A. It helps maintain compliance by reducing exploitable risks and supporting audit-ready security practices.
Comments
Post a Comment