Why SIEM and SOC for MSPs Are Transforming Modern Security Delivery
In today’s evolving threat landscape, SIEM and SOC for MSPs are becoming essential for delivering structured, scalable, and reliable cybersecurity services. Managed Service Providers must protect multiple client environments while maintaining performance, visibility, and compliance. A well-aligned security operations framework enables proactive detection, faster response, and stronger reporting without overwhelming internal teams or increasing operational costs significantly.
Building Strong Foundations with SIEM and SOC for MSPs
SIEM and SOC for MSPs create a centralized approach to monitoring, detection, and response across diverse client infrastructures. By collecting logs from endpoints, cloud platforms, firewalls, and applications, MSPs gain complete visibility into security events. This unified structure helps standardize service delivery, reduce response time, and provide measurable protection outcomes for every managed customer environment.
Key benefits include:
- Centralized monitoring across all client systems
- Faster alert correlation and threat identification
- Standardized response workflows
- Audit-ready compliance reporting
Advancing Threat Protection with Managed MDR for MSPs
Managed MDR for MSPs enhances traditional monitoring by adding proactive threat hunting and expert-driven investigation. Instead of simply generating alerts, MDR solutions analyze attacker behavior patterns, identify advanced threats, and support immediate containment. This layered detection strategy ensures that threats are identified early, reducing business disruption and minimizing potential financial or reputational damage for clients.
Core advantages include:
- Continuous threat hunting across environments
- Rapid containment and guided remediation
- Reduced attacker dwell time
- Access to experienced security analysts
Strengthening Identity Security with Managed ITDR for MSPs
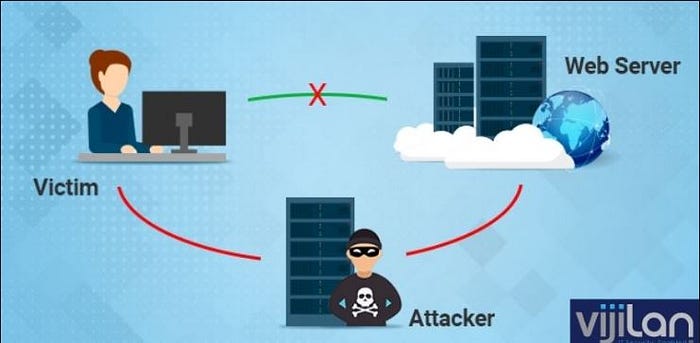
Managed ITDR for MSPs focuses on protecting identity systems, which are frequently targeted by cybercriminals. Compromised credentials and privilege misuse can quickly lead to widespread breaches if left undetected. Identity threat detection continuously monitors login activity, access permissions, and directory behavior to prevent escalation attempts and unauthorized lateral movement across networks.
This approach helps MSPs:
- Detect abnormal authentication attempts
- Monitor directory changes in real time
- Identify privilege escalation risks
- Protect hybrid identity infrastructures
Delivering Practical Protection with Managed SIEM for SMBs
Managed SIEM for SMBs allows smaller organizations to access enterprise-level log monitoring without managing complex infrastructure. It collects and analyzes event data to detect anomalies, generate meaningful alerts, and support incident investigations. This makes advanced security monitoring accessible, affordable, and manageable for growing businesses with limited internal security resources.
Simplifying Deployment with SIEM as a Service for Small Businesses
SIEM as a Service for small businesses provides a cloud-delivered monitoring model that eliminates heavy upfront investments. Organizations can quickly deploy security monitoring without purchasing hardware or managing ongoing maintenance. This subscription-based approach ensures predictable costs while delivering continuous oversight, automated updates, and scalable performance aligned with business growth.
Scaling Efficiently with Cloud-Native SIEM Solution for MSPs
A Cloud-native SIEM solution for MSPs is built for flexibility and rapid scalability. It supports hybrid infrastructures, remote workforces, and expanding data volumes without compromising performance. This architecture enables MSPs to onboard clients quickly, manage high log ingestion rates efficiently, and adapt to constantly changing technology environments with minimal operational friction.
Enhancing Log Visibility with CrowdStrike Falcon LogScale Managed Service
CrowdStrike Falcon LogScale managed service improves high-speed log analysis and search capabilities, enabling security teams to investigate large data volumes efficiently. Faster data processing allows quicker identification of suspicious patterns and anomalies. Advanced log management strengthens detection accuracy and accelerates incident investigations across distributed infrastructures.
Supporting Healthcare Compliance with HIPAA-Compliant SIEM for Healthcare
HIPAA-compliant SIEM for healthcare ensures that access to patient data and electronic health systems is continuously monitored. It maintains detailed audit trails, detects unauthorized activity, and generates compliance-ready reports. This proactive oversight helps healthcare organizations reduce breach risks while aligning security monitoring with strict regulatory requirements.
Protecting Personal Data with GDPR-Compliant SIEM Solution
A GDPR-compliant SIEM solution supports organizations in monitoring access to personal data and identifying potential privacy violations. Continuous logging and alerting mechanisms ensure that data breaches are detected promptly. Proper documentation and reporting workflows help organizations meet regulatory obligations while strengthening overall data protection strategies.
Securing Transactions with SIEM for Financial Services PCI Compliance
SIEM for financial services PCI compliance focuses on protecting cardholder data and transaction systems through continuous monitoring. It detects suspicious payment activities, monitors access to sensitive financial environments, and supports audit preparation. This structured approach enhances trust while ensuring alignment with strict industry compliance standards.
Collaborative Oversight with Co-Managed SIEM for IT Teams
Co-managed SIEM for IT teams, SOC as a Service for SMBs creates a balanced partnership between internal IT departments and external security experts. Organizations maintain operational visibility while benefiting from specialized monitoring and incident response support. This shared model improves knowledge transfer and enhances long-term security maturity.
Continuous Protection Through Managed SOC 24/7 Monitoring
Managed SOC 24/7 monitoring ensures that threats are detected and addressed at any time of day. Continuous oversight significantly reduces the chances of unnoticed breaches. With real-time alerting and structured escalation processes, organizations gain faster response capabilities and stronger resilience against evolving cyber threats.
Reducing Operational Burden with Outsourced SOC Services for SMBs
Outsourced SOC services for SMBs provide expert monitoring without the cost and complexity of building an in-house security operations center. Businesses gain access to skilled analysts, structured response workflows, and advanced detection capabilities while focusing their internal teams on core operational priorities.
Strengthening Collaboration with Co-Managed SOC Services
Co-managed SOC services allow organizations to retain internal oversight while leveraging external expertise for advanced investigations and incident handling. This collaborative model enhances threat detection accuracy, improves response coordination, and builds stronger long-term security processes without fully relinquishing control.
Expanding Capabilities with MSP SOC Multi-Tenant Platform
An MSP SOC multi-tenant platform enables service providers to manage multiple clients within a centralized yet logically separated environment. This structure improves operational efficiency, simplifies onboarding, and ensures standardized security practices while maintaining strict data isolation between customer environments.
Specialized Monitoring with Healthcare SOC HIPAA Compliant
A Healthcare SOC HIPAA compliant framework focuses on protecting sensitive patient records and monitoring regulated healthcare systems continuously. By aligning detection strategies with healthcare compliance standards, organizations reduce regulatory risk while maintaining trust in their digital infrastructure.
Dedicated Oversight with Financial Services SOC
Financial services SOC environments prioritize fraud detection, insider threat monitoring, and protection of transaction platforms. Continuous surveillance and rapid response processes help financial institutions mitigate risks associated with complex digital payment ecosystems and evolving cyber threats.
Safeguarding Confidential Data with Legal Industry SOC Services
Legal industry SOC services focus on protecting confidential case files, client communications, and sensitive documentation. Continuous monitoring of email systems, document repositories, and access controls ensures that law firms maintain strict confidentiality and defend against targeted cyberattacks.
Privacy-Focused Security with GDPR SOC Services
GDPR SOC services emphasize proactive monitoring of personal data access and suspicious activity. By implementing continuous oversight and structured incident response workflows, organizations can quickly address potential data protection incidents and maintain compliance with privacy regulations.
Conclusion
Modern MSPs and SMBs require scalable, compliant, and continuously monitored security operations. Whether through SIEM, SOC, MDR, or identity-focused detection, a layered approach improves visibility, strengthens resilience, and ensures long-term protection in an increasingly complex digital environment.
FAQs
1. What is the difference between SIEM and SOC?
SIEM is a technology platform that collects and analyzes logs, while SOC is the team and process that monitor, investigate, and respond to security alerts.
2. What is SOC as a Service for SMBs?
SOC as a Service for SMBs is a subscription-based security monitoring model where external experts provide continuous threat detection and response without requiring an in-house security team.
Comments
Post a Comment